Wireless Security Wep Key Generator
WEP and WPA are common types of security that are used to protect home wireless networks. When WEP or WPA is turned on ('enabled'), your router uses a special security key combination to allow only. Apr 13, 2012 WiFi (Wireless) Password Security - WEP, WPA, WPA2, WPA3, WPS Explained - Duration: 8:40. How to Find Your Wireless Router IP Address and WEP or WPA key - Duration: 1:41. Nov 11, 2019 WEP stands for Wired Equivalent Privacy, a Wi-Fi wireless network security standard. A WEP key is a security passcode for Wi-Fi devices. WEP keys enable devices on a local network to exchange encrypted (mathematically encoded) messages with each other while hiding the contents of the messages from easy viewing by outsiders. May 16, 2013 Read reviews, compare customer ratings, see screenshots, and learn more about WEP Secure Pro - WEP Key Generator, WPA KeyGen & WiFi Random Password Generator. Download WEP Secure Pro - WEP Key Generator, WPA KeyGen & WiFi Random Password Generator and enjoy it on your iPhone, iPad, and iPod touch. WEP and WPA keys generated by WiFi Password Toolbox generates are supported by most of wireless routers. The WEP/WPA Key Generator supports 128 bit and 64 bit WEP keys, and also support WPA keys for maximum security.WiFi Password Toolbox also generate highly secure and random passwords.
The Firewall.cx Wireless LAN Key Generator will allow the generation of a WEP or WPA ASCII based encryption key and will provide the equivalent HEX or ASCII string so it can be inserted directly into a Cisco Access Point configuration.
Various wireless security protocols were developed to protect home wireless networks. These wireless security protocols include WEP, WPA, and WPA2, each with their own strengths — and weaknesses. In addition to preventing uninvited guests from connecting to your wireless network, wireless security protocols encrypt your private data as it is being transmitted over the airwaves.
Wireless networks are inherently insecure. In the early days of wireless networking, manufacturers tried to make it as easy as possible for end users. The out-of-the-box configuration for most wireless networking equipment provided easy (but insecure) access to a wireless network.
Wireless Security Wep Key Generator Reviews
Although many of these issues have since been addressed, wireless networks are generally not as secure as wired networks. Wired networks, at their most basic level, send data between two points, A and B, which are connected by a network cable. Wireless networks, on the other hand, broadcast data in every direction to every device that happens to be listening, within a limited range.
Wep Security Code
Following are descriptions of the WEP, WPA, and WPA2 wireless security protocols:
Wep Key Generator Online
Wired Equivalent Privacy (WEP): The original encryption protocol developed for wireless networks. As its name implies, WEP was designed to provide the same level of security as wired networks. However, WEP has many well-known security flaws, is difficult to configure, and is easily broken.
Wi-Fi Protected Access (WPA): Introduced as an interim security enhancement over WEP while the 802.11i wireless security standard was being developed. Most current WPA implementations use a preshared key (PSK), commonly referred to as WPA Personal, and the Temporal Key Integrity Protocol (TKIP, pronounced tee-kip) for encryption. WPA Enterprise uses an authentication server to generate keys or certificates.
Wi-Fi Protected Access version 2 (WPA2): Based on the 802.11i wireless security standard, which was finalized in 2004. The most significant enhancement to WPA2 over WPA is the use of the Advanced Encryption Standard (AES) for encryption. The security provided by AES is sufficient (and approved) for use by the U.S. government to encrypt information classified as top secret — it’s probably good enough to protect your secrets as well!
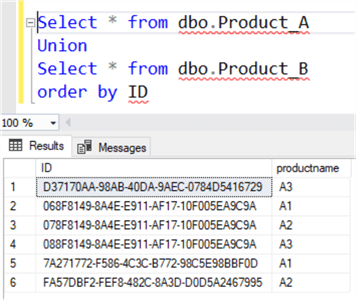
By default, the primary key on a SQL Server table is also used as the clustering key - but that doesn't need to be that way! I've personally seen massive performance gains when breaking up the previous GUID-based Primary / Clustered Key into two separate key - the primary (logical) key on the GUID, and the clustering (ordering) key on a separate INT IDENTITY(1,1) column.