Who Generates A Session Key
A cryptographickey is called ephemeral if it is generated for each execution of a key establishment process. In some cases ephemeral keys are used more than once, within a single session (e.g., in broadcast applications) where the sender generates only one ephemeral key pair per message and the private key is combined separately with each recipient's public key. Contrast with a static key.
Nitro pro 9 serial key generator. Supported: Win / XP / Vista / 7 / 8 / 8.1 / 10 / Mac / iOSNitro PDF Pro 9:Its developed to utilize PDF files perfectly, if you’re searching for Pdf readers, ripper tools and editor there won’t be any best application for you personally except Nitro PDF Pro 9 Crack, and it is the best application for small in addition to large organizations. Category Name: Office Tools. Version: 9. It’s many functions prefer to open, read, create, convert, transfer, edit, sign and smash in to the security on PDF files in protection. Tool Name: Nitro PDF Pro.

Private / public ephemeral key agreement key[edit]
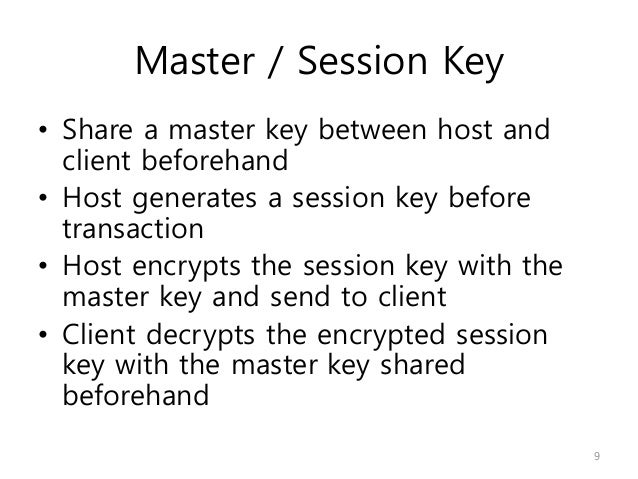
This key is itself then encrypted using the public key. In OpenSSL this combination is referred to as an envelope. It is also possible to encrypt the session key with multiple public keys. This way the message can be sent to a number of different recipients (one for each public key used). The session key is the same for each recipient. Apr 13, 2016 When a request arrives, it contains the username and IP address is automatically recorded. The server then uses the username, the IP address and secret key to re-generate the session Id and see if it matches with the session Id passed by the client. If it does, the verification is successful. With all that said, we can refer back to your question: What key is used to secure the Pre-Shared-Key? In Main Mode, the Pre-Shared-Key (PSK) is verified in Messages 5 and 6. Message 5 and 6 are Protected by the Session keys ISAKMP generates, described above. In Aggressive Mode, none of the messages in the negotiation are encrypted.
Private (resp. public) ephemeral key agreement keys are the private (resp. public) keys of asymmetric key pairs that are used a single key establishment transaction to establish one or more keys (e.g., key wrapping keys, data encryption keys, or MAC keys) and, optionally, other keying material (e.g., initialization vectors).
See also[edit]
External links[edit]
- Recommendation for Key Management — Part 1: General,NIST Special Publication 800-57
Key generators are constructed using one of the getInstance class methods of this class.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys. - Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
As seen in our guides to and how to create a – a public key is in fact just coordinates on the curve calculated through multiplying the generator point by the private key number. Finally, refresh your browser. Generate ethereum address from public key system. Under the Privacy section, click the Content settings button. Under the JavaScript heading, select the Allow all sites to run JavaScript radio button. At the bottom of the page, click the Show advanced settings link.
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
Who Generates A Session Key In Computer
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256