Asa Generating Secret Keys Unknown Encryption Algorithm
Key generation is the process of generating keys for cryptography. The key is used to encrypt and decrypt data whatever the data is being encrypted or decrypted.
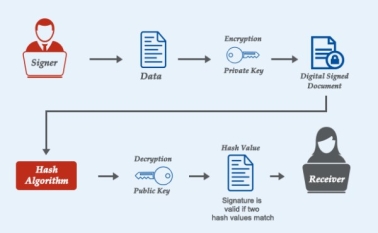
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender will encrypt data with the public key; only the holder of the private key can decrypt this data.
This is the main reason why cryptographers, about 40 years ago, decided that key and algorithm should be split, with the key being secret and the algorithm being non-secret: you can quantify the secrecy of a key, not the secrecy of an algorithm. This gives us an insight into your specific question. How valuable is secrecy of an algorithm? Ask Question Asked 7 years, 4 months ago. Or at least as secret as the password (or the key). In contrast, it is rarely feasible to change the encryption algorithm that is used in a timely fashion, so you have to be able to survive (without loss of security) situations where the algorithm.
Because RSA encryption is a deterministic encryption algorithm (i.e., has no random component) an attacker can successfully launch a chosen plaintext attack against the cryptosystem, by encrypting likely plaintexts under the public key and test if they are equal to the ciphertext.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and its predecessor SSL as well as the SSH use a combination of the two in which:
- One party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data that will be used to generate it).
- The remainder of the conversation (the remaining party) uses a (typically faster) symmetric-key algorithm for encryption.
The simplest method to read encrypted data is a brute force attack–simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer time to attack, making a brute force attack invisible and impractical.
Currently, commonly used key lengths are:
- 128-bits for symmetric key algorithms.
- 1024-bits for public-key algorithms.
Key generation algorithms[changechange source]
In computer cryptography keys are integers. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG), the latter being a computeralgorithm that produces data which appears random under analysis. Some types the PRNGs algorithms utilize system entropy to generate a seed data, such seeds produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess.
In other situations, the key is created using a passphrase and a key generation algorithm, using a cryptographic hash function such as SHA-1.
 Jan 29, 2018 Half-Life 2 Serial Key Download Code Crack key generator Full Game Torrent skidrow Origin Key and Steam Online Code Avaiable. Half-Life 2 Serial Key Cd Key Free Download Crack Full Game Half-Life 2 Serial Cd Key Generator License Activator Product Origin Keys Full. Half-Life 2 free steam key on SteamGateways.com. FREE STEAM GAMES. FREE STEAM KEYS. CD Keys Gift. Instant download. Instant delivery 24/7. FREE Codes & Giveaways. HALF-LIFE sends a shock through the game industry with its combination of pounding action and continuous, immersive storytelling. Valves debut title wins more than 50 game-of-the-year awards on its way to being named. This product is a brand new and unused Half-Life 2 CD Key for Steam. This product is a unique and unused CD Key which can be activated on Steam. After your payment, you will be instantly sent a unique activation code by our automatic delivery system, called 'Autokey'. Jan 09, 2016 Download latest Half-Life 2 cd key generator and generate your own free activation cd key. Redeem your generated product code and play this game online today!! Our team share to you the fresh and updated keygen. We decide to create this key generator to enable fellow gamers to grab a free CD key and play this video game for free of cost.
Jan 29, 2018 Half-Life 2 Serial Key Download Code Crack key generator Full Game Torrent skidrow Origin Key and Steam Online Code Avaiable. Half-Life 2 Serial Key Cd Key Free Download Crack Full Game Half-Life 2 Serial Cd Key Generator License Activator Product Origin Keys Full. Half-Life 2 free steam key on SteamGateways.com. FREE STEAM GAMES. FREE STEAM KEYS. CD Keys Gift. Instant download. Instant delivery 24/7. FREE Codes & Giveaways. HALF-LIFE sends a shock through the game industry with its combination of pounding action and continuous, immersive storytelling. Valves debut title wins more than 50 game-of-the-year awards on its way to being named. This product is a brand new and unused Half-Life 2 CD Key for Steam. This product is a unique and unused CD Key which can be activated on Steam. After your payment, you will be instantly sent a unique activation code by our automatic delivery system, called 'Autokey'. Jan 09, 2016 Download latest Half-Life 2 cd key generator and generate your own free activation cd key. Redeem your generated product code and play this game online today!! Our team share to you the fresh and updated keygen. We decide to create this key generator to enable fellow gamers to grab a free CD key and play this video game for free of cost.
Types Of Encryption Algorithm
Related pages[changechange source]
- Distributed key generation: For some protocols no party should be in the sole possession of the secret key. Rather, during distributed key generation every party obtains a share of the key. A threshold of the participating parties need to work together in order to achieve a cryptographic task, such as decrypting a message.
